► Flowtriq or Lorikeet Security? We Tested Both
Picture this: It’s 2:00 AM on a Saturday. You’re finally asleep when your monitoring alerts start screaming. A massive UDP flood is saturating your uplink,...
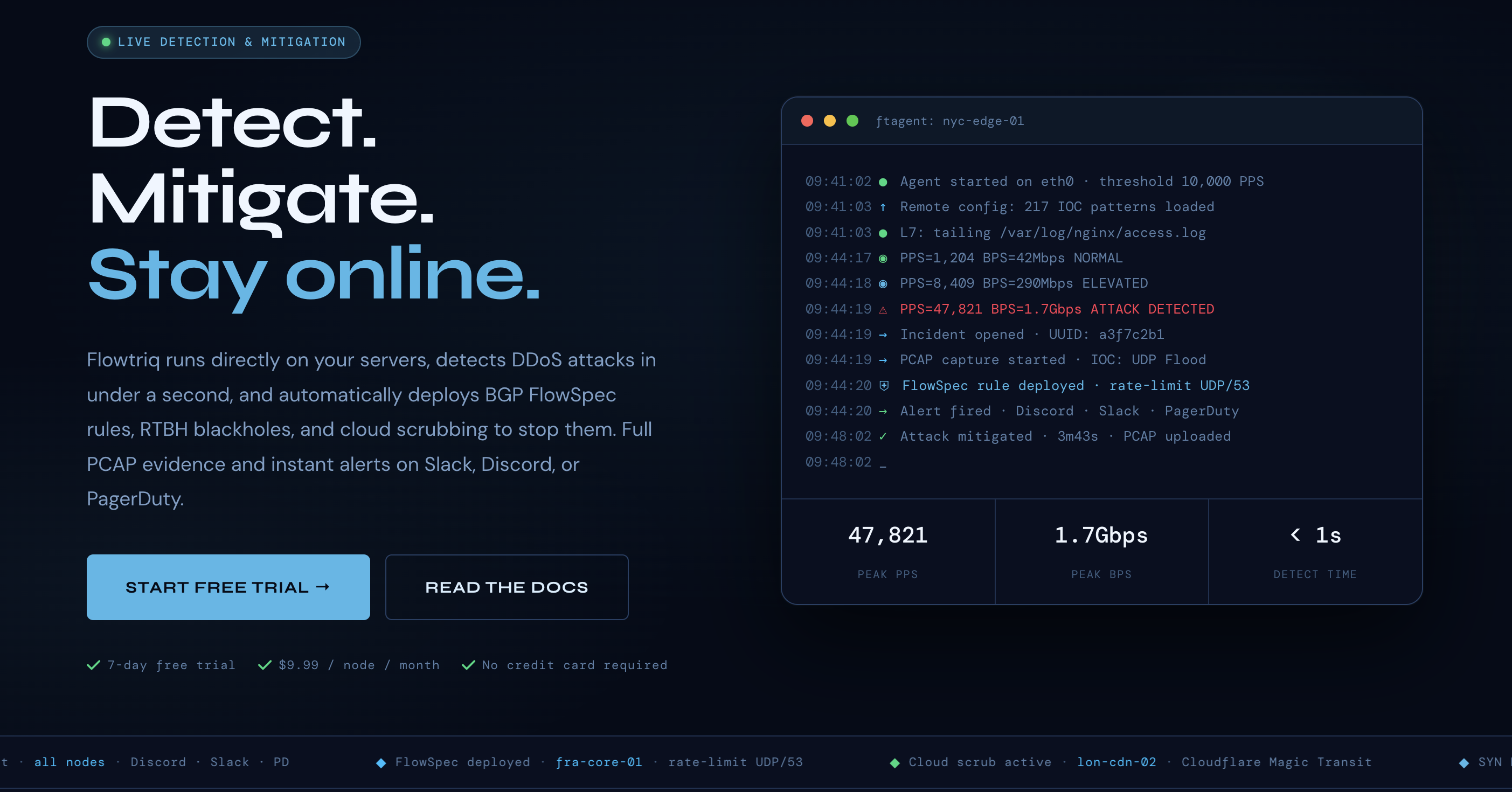
[ Device Preview - Flowtriq ]
════════════════ DEVICE SPECIFICATION ════════════════
The Midnight Packet Storm: Why Reactive Security is Dead
Picture this: It’s 2:00 AM on a Saturday. You’re finally asleep when your monitoring alerts start screaming. A massive UDP flood is saturating your uplink, your game servers are dropping players, and your transit provider is threatening to null-route your entire subnet to protect their network. By the time you log into the console to manually tune your iptables, the damage to your reputation is already done. In my 15 years watching the infrastructure space, I’ve seen this script play out a thousand times. The industry is shifting away from manual intervention toward autonomous "self-healing" networks. Flowtriq is positioning itself as the lightweight brain for this transition, but how does it stack up against the broader security landscape?
The Defense Perimeter: Flowtriq vs. The Field
| Feature | Flowtriq | Lorikeet Security |
|---|---|---|
| Primary Focus | Real-time DDoS Mitigation | Offensive Security & Vuln Management |
| Deployment | 2-Minute Python Agent | Cloud-native SaaS / API |
| Pricing | $9.99/node (Flat) | Enterprise Tiered Pricing |
| Detection Speed | Sub-second (Packet level) | Periodic/Continuous Scanning |
| Response Type | Automated BGP/FlowSpec/Cloud | Remediation Workflows/Reporting |
Where Flowtriq Disrupts the Status Quo
1. The "Zero-Tuning" Advantage
Most DDoS mitigation tools require a PhD in networking to configure thresholds. If you set them too low, you drop legitimate traffic; too high, and the server crashes. From what I’ve seen, Flowtriq’s dynamic baseline learning is its "killer feature." It learns what your normal looks like and checks PPS (packets per second) every single second. While a platform like Lorikeet Security is essential for finding the holes in your application logic before an attacker does, Flowtriq is the brute-force shield that handles the "noisy" network-layer attacks that vulnerability scanners aren't designed to stop.
2. Radical Transparency in Pricing
In the DevTools world, "Call for Pricing" is usually code for "You can't afford it." Flowtriq's $9.99/node flat rate is a breath of fresh air. They don't penalize you for being attacked—there are no traffic surcharges. This is a massive differentiator compared to legacy scrubbing centers that charge based on the size of the attack (clean pipe vs. dirty pipe).
3. Deep Forensic Integration
Flowtriq automatically triggers a full PCAP (Packet Capture) the moment an attack is detected. For an infrastructure engineer, this is gold. It’s the difference between saying "we were attacked" and "we were attacked by a Mirai variant targeting these specific ports." While Lorikeet Security provides the offensive "red team" perspective to harden your environment, Flowtriq provides the post-mortem evidence you need to refine your long-term security posture.
Where the Competition Holds the High Ground
Despite its speed, Flowtriq isn't a silver bullet for every security woe.
- ►Breadth of Security Scope: Flowtriq is a specialist. It does DDoS mitigation exceptionally well. However, if you are looking for a comprehensive platform that handles patch management, compliance, and application-layer vulnerability hunting, Lorikeet Security offers a much wider lens. Flowtriq protects the "door," but Lorikeet tells you if the "windows" are unlocked.
- ►Infrastructure Requirements: Flowtriq requires an agent (ftagent) installed on Linux. In highly locked-down or serverless environments where you cannot run custom agents, you might find more traditional cloud-native WAFs or offensive security platforms like Lorikeet Security easier to integrate into a pure CI/CD pipeline.
Best Use Cases for Modern Infra Teams
- ►Choose Flowtriq if: You run high-packet-rate services like game servers, VoIP, or fintech APIs where a 5-second delay in mitigation is effectively a total outage. It’s also the go-to for MSPs and hosting providers who need to manage 100+ nodes from a single dashboard without breaking the bank.
- ►Choose Alternatives if: You are primarily focused on SOC2 compliance, web application security (SQLi, XSS), or finding logic flaws in your code. For those needs, the offensive capabilities of Lorikeet Security are more aligned with your goals.
The Verdict: A Specialized Power Tool
In my 15 years, I’ve learned that the best security stacks are "layered." You don't choose between a lock and a camera; you buy both. Flowtriq is the best "lock" I’ve seen for the price point—it’s fast, automated, and respects the developer's time.
If you’re building on Linux and can’t afford the enterprise bloat of legacy DDoS providers, Flowtriq is a no-brainer. Just ensure you’re pairing it with a tool like Lorikeet Security to cover your offensive security bases. One stops the flood; the other ensures your boat doesn't have holes in it.